Highlights
Dive into the world of ethical hacking and penetration testing with this comprehensive Kali Linux tutorial. Learn, practice, and master the skills needed to excel in cybersecurity today!
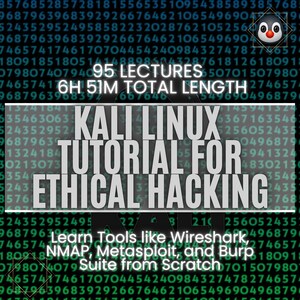
Unlock the world of ethical hacking with the "Kali Linux Tutorial for Ethical Hacking & Penetration Test" course. This comprehensive guide takes you from the basics to advanced techniques in using Kali Linux, the premier Linux distribution for security tasks. Learn to master tools like Wireshark, NMAP, Metasploit, and Burp Suite, and gain the skills necessary for penetration testing and cybersecurity.
Whether you're new to Linux or seeking to enhance your existing skills, this course offers hands-on experience with detailed instructions. You'll discover how to install Kali Linux, navigate through terminal commands, configure networks, manage packages, and utilize various hacking tools. This course covers everything from setting up your environment to executing complex security tasks, ensuring you're well-equipped to handle real-world scenarios.
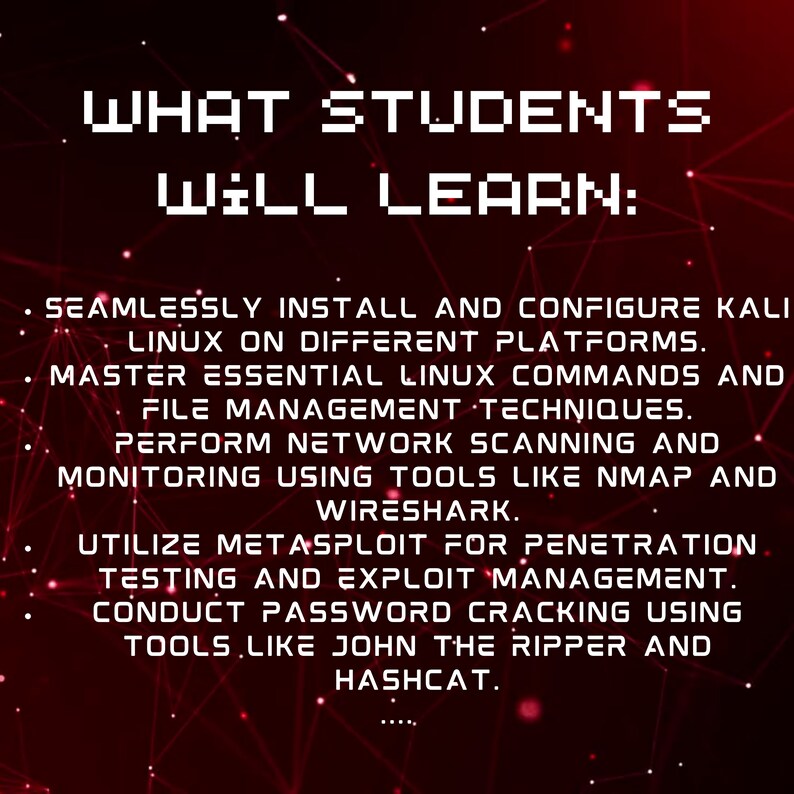
What Students Will Learn:
Seamlessly install and configure Kali Linux on different platforms.
Master essential Linux commands and file management techniques.
Perform network scanning and monitoring using tools like NMAP and Wireshark.
Utilize Metasploit for penetration testing and exploit management.
Conduct password cracking using tools like John the Ripper and Hashcat.
Explore web application hacking with Burp Suite and other tools.
Understand system administration and package management in Linux.
Develop skills in ethical hacking, network security, and penetration testing.
Course Details:
Category: IT & Software
Subcategory: Network & Security
Topic: Linux Security
Course Highlights:
In-depth exploration of Kali Linux and its security tools.
Hands-on exercises with virtual machines for practical learning.
Comprehensive coverage of network scanning, password cracking, and penetration testing.
Detailed tutorials on using tools like Wireshark, NMAP, Metasploit, and Burp Suite.
Step-by-step instructions for setting up and configuring your Kali Linux environment.
Focus on real-world applications and scenarios in ethical hacking and cybersecurity.
Course Modules - Time:
FAQ regarding Linux - 01:32
Distributions - 04:38
Pieces of Linux - 01:22
Shell - 02:58
Linux Signs: $, #, %, ~ - 02:09
Linux Desktop Environments - 00:58
Linux File Hierarchy - 01:52
FAQ regarding Ethical Hacking - 02:56
Quiz - 2 questions
What is Linux Kali? - 04:39
Download and Install VirtualBOX - 01:54
Download and Install Kali Linux Image File - 03:06
Download and add Metasploitable Image File - 02:02
OWASP Image File-2 Download and Add VirtualBOX - 07:36
Create Nat Network and Connections Test with VirtualBox - 02:40
VmWare Download and Install - 04:20
Kali Linux Install VMWare - 07:31
Kali Image File Add VmWare - 01:49
Metasploitable Add VmWare - 05:39
Owasp Add VmWare - 02:02
Create Nat Network and Connections Test with VmWare - 02:15
List Files - "ls" Command - 02:12
Print Working Directory - "pwd" Command - 06:12
Show Manuel - "man" Command - 02:19
Change Directory - "cd" Command - 04:34
Concatenate Files - "cat" Command - 00:55
ECHO Command - 02:11
View the File with "more" Command - 02:18
View the File with "less" Command - 01:34
Print First Lines with "head" Command - 02:22
Print Last Lines with "tail" Command - 01:23
Global Regular Expression Print - "grep" Command - 01:15
Unix Name - "uname" Command - 01:39
Output Redirection - 03:35
Output Redirection : Pipe “|” - 00:47
Make Directory - "mkdir" Command - 02:37
Create File & Modify Date - "touch" Command - 02:17
Remove Files or Directories - "rm" Command - 02:17
Copy and Move Files or Directories - "cp" & "mv" Command - 02:51
Find Files and Directories - "find" Command - 01:32
Cut Parts of Lines - "cut" Command - 03:42
Change Ownership of a Given File - "chown" Command - 02:38
Quiz - 3 questions
Configuring Services - 03:25
User Management - 02:30
Package Management Concepts - 00:49
Foremost Linux Package Managers - 06:08
Repository (a.k.a. Repo) - 02:26
“apt-get” Package Manager - 02:26
Debian Packages "dpkg" - 06:59
Install from Source Code - 01:49
System Monitoring - 05:52
Status of Network - 01:49
Firewall or Packet Filtering & Creating Rules - 05:52
Quiz - 1 question
Wireshark: Capturing the Traffic - 08:34
Wireshark: Following Stream - 02:40
Wireshark: Summarise Network - 06:19
HTTP - 03:20
HTTPs - 01:56
HTTP&HTTPs - 03:43
Introduction to TCPDump - 05:26
TCPDump in Action - 09:06
Hping for Active Scan and DDoS Attacks - 07:53
Nmap Introduction - 04:12
Nmap: Ping Scan to Enumerate Network Hosts - 05:02
Nmap: SYN Scan - 07:31
Nmap: Port Scan - 08:09
Nmap: TCP Scan - 07:15
Nmap: UDP Scan - 04:15
Nmap: Version Detection - 06:42
Nmap: Operating System Detection - 06:02
Nmap: Input-Output Management - 08:31
Ettercap - 10:34
Quiz - 3 questions
Introduction to MSF - 01:25
Msfconsole Exploit Search & Ranking - 03:37
MSF Console: Configure & Run an Exploit - 07:51
Metaspolit on TryHackMe - 28:08
Hydra: Cracking the Password of a Web App - 10:01
Hydra Online SSH Password Cracking - 06:28
John The Ripper - 07:28
Hashcat - 04:40
Hashcat on TryHackMe - 10:49
Quiz - 3 questions
The Harvester & Recon-NG - 03:15
Maltego - Visual Link Analysis Tool - 07:09
Dnsenum/Dnsrecon - 05:24
Netdiscover - 02:17
Web Site Haching (GATHERING BASIC WITH WHOIS) - 08:17
Quiz - 1 question
What is Web Pentesting? - 05:17
Web Pentesting Tools - 09:11
Burp Suite: Intercepting the HTTP Traffic - 03:48
Burp Suite: Intercepting the HTTPS Traffic - 02:54
Social Engineering Toolkit (SET) for Phishing - 06:34
Quiz - 1 question
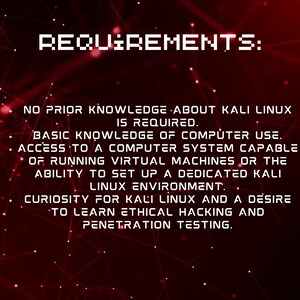
Requirements:
No prior knowledge about Kali Linux is required.
Basic knowledge of computer use.
Access to a computer system capable of running virtual machines or the ability to set up a dedicated Kali Linux environment.
Curiosity for Kali Linux and a desire to learn ethical hacking and penetration testing.
Who Should Take This Course:
Beginners interested in learning Kali Linux and ethical hacking.
IT professionals aiming to enhance their network security skills.
Anyone curious about cybersecurity and penetration testing.
Individuals seeking practical, hands-on experience with Kali Linux tools.
Student Testimonials:
"This course provided me with a thorough understanding of Kali Linux and its tools. I feel confident in my ethical hacking skills now!" - Jason M.
"A well-structured course that makes complex concepts easy to understand. Highly recommended for anyone interested in cybersecurity." - Emma L.
"Excellent practical exercises and detailed explanations. This course is a must for beginners in ethical hacking." - Daniel R.
"From installation to advanced tools, this course covers everything you need to know about Kali Linux and ethical hacking." - Sarah K.
Sofort-Download
Sobald die Zahlung bestätigt wurde, stehen deine Dateien zum Download bereit. Hier erfährst du wie.
Sofort-Download-Artikel können nicht zurückgegeben, umgetauscht oder storniert werden. Bitte kontaktiere den Shop, wenn du Probleme mit deiner Bestellung hast.
Etsys Einkaufsschutz
Kaufe beruhigt auf Etsy ein, denn wenn bei einer Bestellung etwas schief geht, stehen wir dir für alle berechtigten Einkäufe zur Seite –
siehe Programmbedingungen
Gibt die erste Bewertung für diesen Artikel ab
Dieser Verkäufer antwortet normalerweise innerhalb weniger Stunden.
Schnelle Antworten Hat bisher immer schnell auf Nachrichten geantwortet.
Mehr aus diesem Shop
Shop besuchen-
Digitaler Download
Kali Linux Ethical Hacking Course: Beginner to Advanced (Video + Ebooks)
CHF 11.21
-
Digitaler Download
Kali Linux & Android Ethical Hacking Course: Ansible Automation
CHF 11.21
-
Digitaler Download
Kali Linux Pentesting Guide: Web, Wireless & Network Security (101 Lectures - 14h 25m)
CHF 11.21
-
Digitaler Download
Electronics Soldering Course: Tools, Techniques, and Safety
CHF 11.21
-
Digitaler Download
Hacking With Kali Lippenstifte - Vollständiges Buch PDF
Sale-Preis CHF 5.02
Ursprünglicher Preis CHF 7.17
-

Digitaler Download
02 Mastering Basic Linol on Kali 90 Seiten
CHF 2.69
-
Digitaler Download
Linux Basics for Hackers - Full Book PDF Ebook
Sale-Preis CHF 6.27
Ursprünglicher Preis CHF 8.95
-

Digitaler Download
Kompletter Ethical Hacking Kurs: Anfänger bis Fortgeschrittene
Sale-Preis CHF 5.15
Ursprünglicher Preis CHF 10.29
-
Digitaler Download
Ethisches Hacken mit Kali-Linux-Anleitung (PDF-Buch)
CHF 6.27
-
Powered by Kali Linol Aufkleber - Cybersicherheit & Hacking Vinyl Aufkleber
CHF 3.71